
Secrets of Corporate Bug Sweeping Every Executive Should Know
Corporate espionage isn’t a plot from a streaming thriller; it’s a line item on real security risk assessments. Boardroom discussions cover M&A plans, product roadmaps, market-entry strategies, and confidential legal issues—the kind of intel competitors or hostile actors would pay handsomely to hear.
A leaked conversation isn’t just embarrassing. It can derail negotiations, wipe millions off a company’s valuation, or give competitors an edge that’s impossible to claw back. In high-value industries like finance, biotech, defense, and tech, this kind of breach can even lead to regulatory scrutiny and shareholder lawsuits.
Technical Surveillance Counter-Measures (TSCM), once the domain of intelligence agencies, are now a standard part of the corporate security toolkit. While security teams or specialist consultants handle the day-to-day sweeps, every executive should understand what these tools do, when they should be deployed, and how to interpret the results.
Below are six essential tools to have in your boardroom security playbook, along with practical insights into why they matter, how they work, and what could happen without them.
1. Phone Safes: Cutting Off the Cellular Eavesdropper
.jpg)
Secure phone storage(1)
If a phone is on, it can be used as a microphone. That’s not paranoia; multiple intelligence leaks have shown remote mic activation is real—even when a handset looks powered down. Smartwatches, SIM-enabled tablets, and other connected gadgets can be turned into listening posts too.
What It Does
Rather than blocking the signal, a phone safe targets the microphones themselves. It emits non-filterable ultrasonic interference that overwhelms both primary and secondary mics. Result: no intelligible audio to capture or transmit—even if malware tries.
Why It Matters
Since the Snowden era, we’ve known about remote mic activation. And in some jurisdictions, close ties between carriers and government make mobile traffic an easy target.
Executive Takeaway
Choose portable units for travel and fixed installs for permanent rooms. If you’re meeting abroad—or in countries with active corporate spying—bring the portable model with the security team.
2. IR Camera Detectors: Seeing the Invisible

Hidden camera lens detector(2)
Tiny cameras are cheap, easy to hide, and stream crisp video over Wi-Fi. But even the most advanced hidden cameras share one weakness: lenses reflect infrared light—even in standby or "off.”
What It Does
IR detectors sweep the room with infrared/laser-assisted optics to catch that telltale lens glint. Lights stay on; the scan still works.
Why It Matters
In 2019, South Korean police found a network of covert hotel cameras live-streaming more than 1,600 guests. Swap "tourists” for "executives” and you see the risk.
Executive Takeaway
Fast, discreet, and perfect for a pre-meeting check. A trained operator can clear a room in minutes when schedules are tight.
3. RF Detectors: The Signal Hunters

Multiband RF detector(3)
While phone safes neutralize microphones, RF detectors do something different. They expose all active transmissions from devices, whether audio, video, or data. They are basically the bloodhounds of the TSCM world.
What It Does
They scan the radio spectrum for anomalies like Bluetooth bugs, Wi-Fi cams, GSM transmitters, and even devices that burst traffic intermittently to dodge detection.
Why It Matters
In 2014, the European Central Bank disclosed the discovery of wireless bugs in its conference rooms—devices placed there to eavesdrop on critical policy discussions. RF detection was key to finding them by detecting their transmissions.
Executive Takeaway
Not every signal is a threat; offices are noisy by design. You need trained TSCM operators who can separate everyday chatter from suspicious emissions. IT staff are usually not equipped for the task.
4. Encrypted Communication Apps: Keeping the Conversation Clean
Locking down your physical space only solves half the problem. Your conversations are still vulnerable to interception when traveling over unprotected channels. Email, standard SMS, and unencrypted calls are soft targets.
What It Does
Encrypted communication apps, such as Signal, Wickr, and Threema, use end-to-end encryption to ensure only the intended recipients can read or hear messages. Many also offer disappearing messages, screenshot alerts, and secure file sharing.
Why It Matters
U.S. court filings in 2022 underscored how unprotected business comms are routinely accessed through warrants by the FBI. In regulated industries, losing control of communications can also trigger GDPR issues and heavy fines.
Executive Takeaway
Choose apps that support policy control and secure backups. Training is necessary because an encrypted app is useless if executives accidentally route sensitive files through unsecure channels.
5. Ultrasonic Microphone Jammer: Silencing Hidden Ears
.jpg)
Ultrasonic microphone jammer(4)
Sometimes, it’s just not possible or realistic to locate every listening device. So, your next line of defense is to render microphones useless.
What It Does
An ultrasonic jammer emits sound waves outside the range of human hearing that directly interfere with the way microphones work. They overwhelm both primary and secondary mics, preventing them from capturing clear speech. Even if a device is hacked or fitted with advanced filtering software, the interference ensures that nothing usable is recorded.
Why It Matters
Unlike traditional white noise generators, ultrasonic systems target microphones, not the audible spectrum. So even modern AI audio-cleaning tools are ineffective against them. They create an invisible shield around the conversation that blocks the raw input before it can ever be transmitted.
Executive Takeaway
Omni Tower units—full-size or mini—fit boardrooms, hotel suites, and other temporary spaces where trust is low. Deploy them alongside other TSCM tools for layered protection.(4)
6. DRUID Conversation Protectors: Creating a Secure Speech Zone
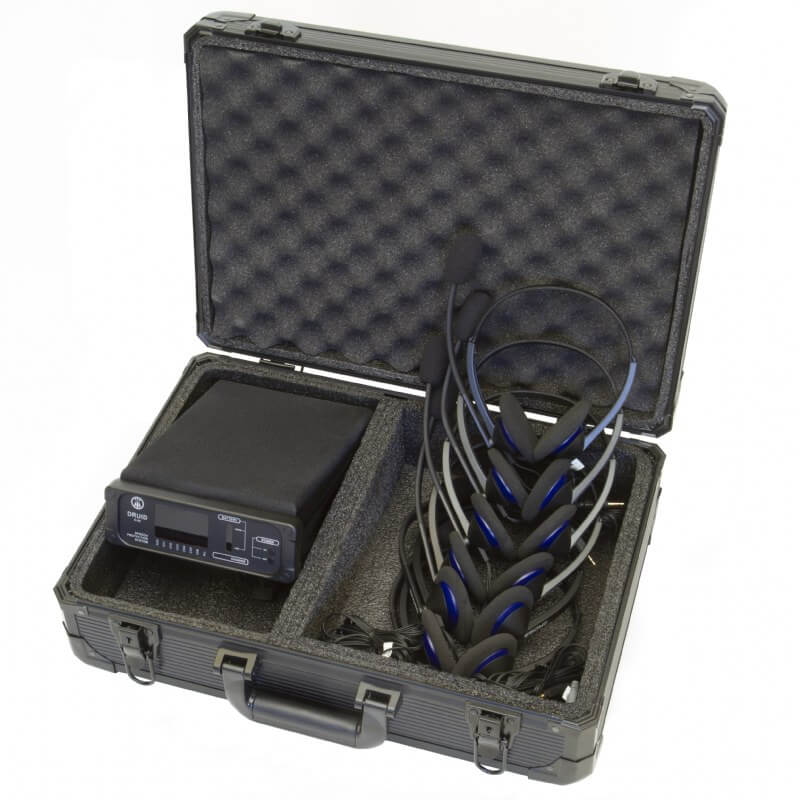
Conversation protector(5)
Omnidirectional speakers protect the whole room. DRUID takes a more surgical route.
What It Does
DRUID uses directional speakers and ultrasonic masking to create a small "speech privacy zone” around meeting participants. Any microphone outside this zone hears nothing but scrambled noise. Meanwhile, the conversation inside the zone remains crystal clear.
Why It Matters
Perfect for ad-hoc meetings in rented venues, hotels, or co-working spaces where you can’t vouch for the environment.
Executive Takeaway
Portable, battery-powered DRUID units can be deployed in minutes. Security-conscious executives keep them in travel kits, especially when attending off-site strategy sessions or international negotiations.
The Cost of Doing Nothing
- Undermine shareholder confidence.
- Jeopardize ongoing mergers or partnerships.
- Invite regulatory action if data protection laws are violated.
- Damage brand reputation in ways that take years to repair.
Building a Boardroom Security Protocol
- Routine sweeps before and after high-level meetings.
- Training for executives on safe communication practices.
- Travel protocols for meetings abroad, including portable GSM, DRUID, and IR scanning equipment.
- Secure storage for sensitive documents and devices during meetings.
- Regular updates to security equipment are crucial because surveillance technology evolves quickly, and outdated tools can give a false sense of safety.
Final Word: Awareness Is Your First Layer of Defense
FAQ: Boardroom Security & TSCM Tools
What does TSCM stand for?
Do only large corporations need TSCM tools?
How often should boardrooms be checked for surveillance devices?
Can a Phone safe block all types of eavesdropping?
Are IR camera detectors foolproof?
What’s the difference between omni-channel speakers and DRUID systems?
- Omni-channel speakers flood an entire room with layered noise to mask speech.
- DRUID conversation protectors create a focused, private "speech zone” around a small group of people, making them better for portable or ad-hoc use.
Does end-to-end encryption solve the problem?
How much do professional TSCM sweeps cost?
What’s the biggest mistake companies make in boardroom security?
Can TSCM tools be used internationally?
References
- (1) Secure Phone Storage — Phone Safe Summit
- (2) Hidden Camera Lens Detector — OPTIC-2
- (3) Multiband RF Detector — iProtect 1217
- (4) Ultrasonic Microphone Jammer — Omni Tower / Omni Tower Mini
- (5) Conversation Protector — DRUID D-06
Damir First
CEO of SpyShopEurope.com
Request a custom quote for a personalized recommendation.




